Hi, what do you want to do?
Curated Video
CompTIA Security+ Certification SY0-601: The Total Course - Defining a Public Server
Public servers offer services to internet users. These servers should be hardened and placed on an isolated network such as a screened subnet or DMZ so that in the case of compromise, lateral movement by the attacker will not allow...
Curated Video
CompTIA Security+ Certification SY0-601: The Total Course - hping3 Forged Packet Lab
The hping3 tool provides many services, including the creation of network packets based on command-line parameters. This episode demonstrates craft packets using the hping3 tool.
This clip is from the chapter "Testing...
This clip is from the chapter "Testing...
Curated Video
CompTIA Security+ Certification SY0-601: The Total Course - Chapter 7 Ask Me Anything (AMA)
Some wireless networking attacks involve deception. In this episode, Mike describes how there are variations of Evil Twin attacks including through DNS.
This clip is from the chapter "Securing Wireless LANs" of the series...
This clip is from the chapter "Securing Wireless LANs" of the series...
Curated Video
SSL Complete Guide 2021: HTTP to HTTPS - Elliptic Curve Cryptography Overview
In this video, we'll learn about elliptic curve cryptography.<br/<br/>>
This clip is from the chapter "SSL, TLS, and HTTPS" of the series "SSL Complete Guide 2021: HTTP to HTTPS".In this section, we'll learn about SSL, TLS, and HTTPS.
This clip is from the chapter "SSL, TLS, and HTTPS" of the series "SSL Complete Guide 2021: HTTP to HTTPS".In this section, we'll learn about SSL, TLS, and HTTPS.
Curated Video
CompTIA Security+ Certification SY0-601: The Total Course - Hypervisors and Virtual Machines
Hypervisors are servers configured to host virtual machine guests. This episode will discuss Type 1 and Type 2 hypervisors as well as hardening. This clip is from the chapter "Securing Public Servers" of the series "CompTIA Security+...
Curated Video
CompTIA Security+ Certification SY0-601: The Total Course - Threat Analysis and Mitigating Actions
Stepping through how attackers manage to compromise a system or exfiltrate data helps harden environments to prevent future incidents. This episode covers the Cyber Kill Chain, the Mitre ATT&CK Framework, the Diamond Model of Intrusion...
Curated Video
CompTIA Security+ Certification SY0-601: The Total Course - Social Engineering
Tricking people into doing something or divulging sensitive information – this is social engineering. This episode discusses a pretext, or believable story, that often goes along with this type of activity.
This clip is...
This clip is...
Curated Video
CompTIA Security+ Certification SY0-601: The Total Course - Data Backup
Backing data up provides availability in the event of data deletion, corruption, or encryption through ransomware. This episode discusses backup settings such as compression and encryption, as well as full, differential, and incremental...
Curated Video
CISSP® Certification Domain 1 Security and Risk Management Video Boot Camp for 2022 - International Agreements and Guidelines
This video highlights the international agreements and guidelines.
This clip is from the chapter "Certified Information Systems Security Professional CISSP Domain 1 - Security and Risk Management" of the series "CISSP®...
This clip is from the chapter "Certified Information Systems Security Professional CISSP Domain 1 - Security and Risk Management" of the series "CISSP®...
Curated Video
CompTIA Security+ Certification SY0-601: The Total Course - Physical Security
This episode covers physical security controls such as door lock types and bollards, as well as encryption of data at rest.
This clip is from the chapter "Physical Security" of the series "CompTIA Security+ Certification...
This clip is from the chapter "Physical Security" of the series "CompTIA Security+ Certification...
Zach Star
This completely changed the way I see numbers - Modular Arithmetic Visually Explained
This completely changed the way I see numbers - Modular Arithmetic Visually Explained
Zach Star
Computer Science Careers and Subfields
This video will cover computer science careers and as well as different areas within computer science you can dive into. Computer science is a very broad and diverse field that includes software...
PBS
Cyber Codes
Let's get the video out in the open. Viewers learn about some early instances of cryptography and then hone in on modern cyber codes. Specifically, the animated video describes the basics of how public key cryptography works.
Physics Girl
Quantum Cryptography Explained
Cryptography keeps your identifying information safe! An interesting lesson explains the history of encryption and decryption. The instructor begins with simple strategies and progresses to quantum cryptography to finish the well-rounded...
Code.org
The Internet: Encryption and Public Keys
We can partially thank Caesar that our e-mails are secure! Viewers learn how encryption and public key cryptography keep our communications safe over the Internet. The video also briefly covers the history of ciphers, such as the Caesar...
TED-Ed
Is DNA the Future of Data Storage?
When you think of secret messages and data storage, DNA doesn't normally come to mind. Viewers watch a video that explains how scientists use DNA to store information. It describes some recent advances in the area.
Domain of Science
The Map of Mathematics
How does all this math fit together? The resource creates a graphical view of the extent of mathematics. The map shows the pure and applied sides of studying mathematics and breaks them down into their many disciplines.
Crash Course
Cryptography: Crash Course Computer Science #33
Uncover key concepts in cryptography in the 33rd installment of a computer science series. An engaging video describes various encryption methods. It explains substitution ciphers, permutation ciphers, the Enigma machine, advanced...
Massachusetts Institute of Technology
Mit: Blossoms: Fabulous Building Cryptosystems
As part of this introduction to cryptography, students will build three devices and learn how to encrypt and decrypt messages. Video is accompanied by a teacher's guide, transcript, and other handouts, as well as links for learning more...
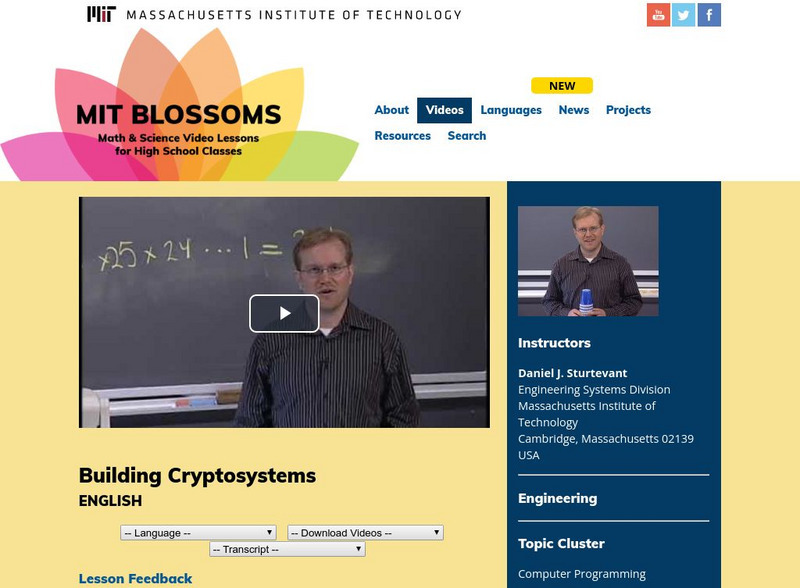
Massachusetts Institute of Technology
Mit: Blossoms: Building Cryptosystems
This video module presents an introduction to cryptography - the method of sending messages in such a way that only the intended recipients can understand them. In this very interactive lesson, students will build three different devices...
Massachusetts Institute of Technology
Mit: Blossoms: The Mathematics of Cryptography
This video lesson provides a more advanced approach to cryptography than the more experiential Sturtevant cryptography lesson also in the BLOSSOMS video library. Students will learn about the history of cryptography, and they will also...
Annenberg Foundation
Annenberg Learner: Mathematics Illuminated: The Primes
A detailed look at the importance of prime numbers, not only in math, but also in science and in the field of cryptography. [28:27]
Crash Course
Crash Course Computer Science #33: Cryptography
This episode discusses how to keep information secret using cryptography. From as early as Julius Caesar's Caesar cipher to Mary, Queen of Scots, encrypted messages to kill Queen Elizabeth in 1587; there has long been a need to encrypt...