Hi, what do you want to do?
Global Ethics Solutions
Understanding Confidentiality & IP: Ethical Issues | Part 1
Part 1 introduces confidentiality and intellectual property basics. Learn how to protect trade secrets, sensitive information, and avoid misuse in the workplace.
Global Ethics Solutions
Ethical Expectations: Code of Conduct Training | Part 3
Explore ethical decision-making in handling confidential info, trade secrets, and business gifts in Part 3 of our Code of Conduct training series.
Curated Video
Learn English Words: Confidential
The goal of the GCF Reading Program is to help adults at all levels become more proficient readers.
Utilizing various learning tools, learners will be able to learn and practice reading the top 1,000 most frequently used...
Utilizing various learning tools, learners will be able to learn and practice reading the top 1,000 most frequently used...
Curated Video
Risk Management for Cyber Security Managers - Information Classification
In this lesson, you will learn how to classify information to understand how to mitigate risks in the most efficient manner.
Curated Video
CISSP Crash Course - Information Assets
This video explains information assets and data classification.
<
br/>
This clip is from the chapter "Asset Security" of the series "CISSP Crash Course".This section covers domain 2, which focuses on asset security, data, and...
<
br/>
This clip is from the chapter "Asset Security" of the series "CISSP Crash Course".This section covers domain 2, which focuses on asset security, data, and...
Curated Video
Hack Using Google ONLY
You will learn how to easily perform hacking using search engines and publicly available information. Find passwords, confidential files, and gain access to systems with minimum efforts.
Curated Video
Google Dorks Live Examples
Spot the vulnerabilities in the wild, leverage Google to hack into web applications and systems that are published over the Internet. You will be surprised by how easy it is.
Curated Video
LAB 2: Google Hacking
I will show you the basics of Google hacking without any prior technical knowledge
Global Ethics Solutions
Protecting Confidential Information and Ethical Gift Giving in Business
This presentation introduces participants to various ethical decision-making models and then expands to cover common code of conduct topics. The emphasis of this course is to help employees develop solid ethical decision-making skills in...
Global Ethics Solutions
Understanding Confidentiality and Intellectual Property Ethical Issues and Problems
This presentation helps viewers understand confidential information, trade secrets, and intellectual property as well as the costs of protecting intellectual property.
ShortCutsTv
Ethical Issues in Psychological Research
This film looks at the nature and significance of ethical guidelines to the research process, using examples drawn from the work of Milgram, Watson and Sharif.
Global Ethics Solutions
Understanding Confidentiality and Intellectual Property Issues and Problems (Part 1)
This presentation helps viewers understand confidential information, trade secrets, and intellectual property as well as the costs of protecting intellectual property.
Seven Dimensions
Respecting Privacy and Confidentiality at Work
This video discusses the difference between privacy and confidentiality and provides tips on how to respect and maintain both in a work setting.
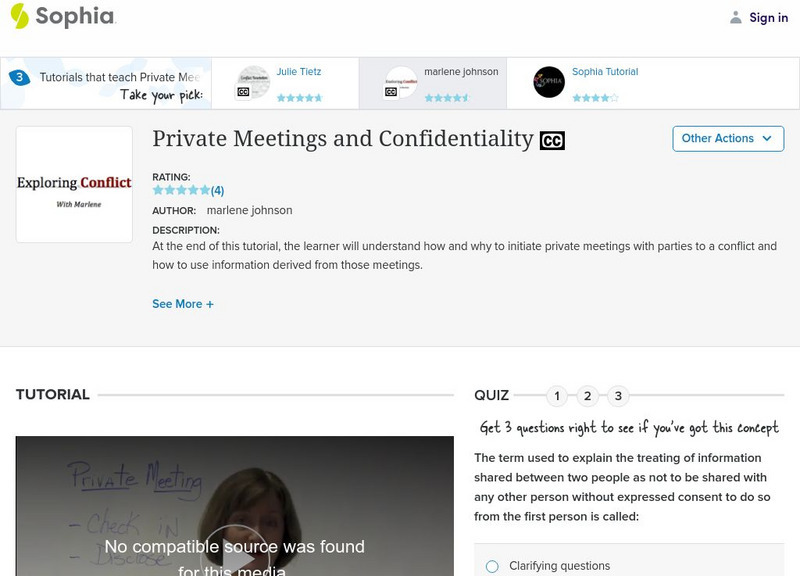
Sophia Learning
Sophia: Private Meetings and Confidentiality
At the end of this tutorial, the learner will understand how and why to initiate private meetings with parties to a conflict and how to use information derived from those meetings. It includes a video, a video transcript, a quiz, and...