Hi, what do you want to do?
Be Smart
The Mathematical Code Hidden In Nature
How do zebras get their stripes? How do leopards get their spots? And how do giraffes get their giraffe-shaped thingies, whatever they are called? Would you believe the answer is… math? This is the story of a WWII wartime codebreaker and...
SciShow
SciShow Quiz Show with Phil Plait: Sperm, Whales, and Sperm Whales
Hank and Phil Plait dive deep into questions about gametes and sea mammals in this episode of SciShow Quiz Show!
Curated Video
Navajo Code Talkers for Kids | Bedtime History
Learn about the Navajo Code Talkers, who served valiantly during World War II.
Curated Video
AWS Certified Solutions Architect Associate (SAA-C03) - Multi-Factor Authentication
What if you don't trust a single authentication method, such as a username and password pair? Then you can use multi-factor authentication, which is presented in this video.
Curated Video
How to Make Simple a Secret Decoder
People have been using codes throughout history to keep their messages private and my two little spies needed a way to sent their secret messages to each other too. So I came up with this simple paper plate decoder for them to have fun.
Curated Video
How Queer Communities Created Secret Languages
Across the globe, queer communities have relied on secret lexicons known as "argots" to communicate safely, which have developed over the years into what some call "verbal jazz."
The Guardian
Free improvisation: still the ultimate in underground music?
Pioneered in the 1950s by musicians breaking the rules of jazz and composition, free improvisation is still as difficult – and potentially transcendent – as it ever was. A Guardian documentary takes you inside its world, talking to...
Religion for Breakfast
The Origins of the Jesus Fish
In this episode we examine the topic: The Origins of the Jesus Fish
Programming Electronics Academy
Easy secret knock detector to trigger anything with only an Arduino and a few cheap components
There are a couple good use case scenarios for making a secret knock detector using an Arduino.
Packt
CompTIA Network+ Certification N10-007: The Total Course - Identification
This video shows how to perform identification. This clip is from the chapter "Securing Transmission Control Protocol/Internet Protocol (TCP/IP)" of the series "CompTIA Network+ Certification N10-007: The Total Course".In this section,...
Curated Video
AWS Solutions Architect Associate (SAA-C02) Exam Prep Course - 2021 UPDATED! - Multi-Factor Authentication
This video explains the multi-factor authentication process.
This clip is from the chapter "Solutions Architect Chapter 7 - Identity and Access Management (IAM)" of the series "AWS Solutions Architect Associate (SAA-C02)...
This clip is from the chapter "Solutions Architect Chapter 7 - Identity and Access Management (IAM)" of the series "AWS Solutions Architect Associate (SAA-C02)...
Extra English Practice
Pronouncing S and SH
English pronunciation lesson showing the difference between theS and SH sounds. Includes tongue twister and interactive game for practice.
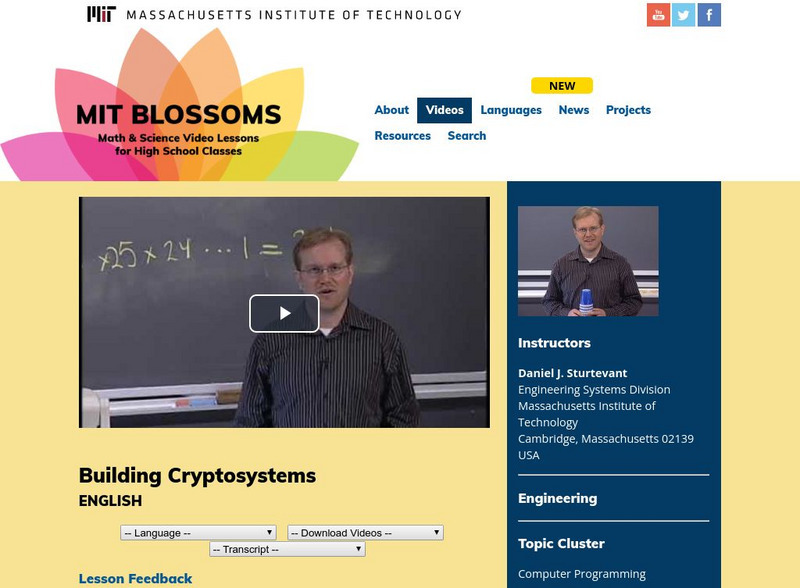
Massachusetts Institute of Technology
Mit: Blossoms: Fabulous Building Cryptosystems
As part of this introduction to cryptography, students will build three devices and learn how to encrypt and decrypt messages. Video is accompanied by a teacher's guide, transcript, and other handouts, as well as links for learning more...
British Council
British Council: Learn English Kids: Spycat
Listen to and read along with an animated story about Spycat, who follows clues to find the evil Ratty before he can release a computer virus. Help Spycat follow the clues by unscrambling words and breaking a secret code.