Code.org
Cracking the Code
Scholars learn how to crack secret codes as they continue reading from the Blown to Bits and try to crack the random substitution cipher. They also begin learning about the Vigenere cipher.
Institute of Electrical and Electronics Engineers
Binary Basics
Back to the (binary) basics. The resource provides a simple overview of binary code and gives two different activities to introduce it to elementary and middle school learners. Classmates write and decode messages to each other in binary...
Anti-Defamation League
Student Dress Codes: What's Fair?
The controversy over school dress codes continues. The debate involves questions like, why is there a policy? Who sets the policy? Who enforces the policy? What is a fair policy? Tweens and teens have an opportunity to engage in the...
Doing Maths
Converting Metric Measurements Code-Breaker
Can your scholars crack the code of this metric activity? To start, mathematicians must convert different units of measurement to the standard metric system form. Then, pupils plug in the corresponding letter to the correct answer to...
Core Knowledge Foundation
Unit 8: Code Talker by Joseph Bruchac Teacher Guide
Joseph Bruchac's Code Talker tells the remarkable story of Navajo Marines' role in battles of the Pacific Theater during World War II. As scholars read the novel, they also engage in activities that expand their knowledge of Navajo...
National Park Service
Lesson 5: Coded Spirituals, Metaphor in African Spirituals
If a picture is worth a thousand words, song lyrics also can communicate many meanings. Using the lyrics of spirituals, young historians analyze them for coded messages about freedom. Resources include a chart to help individuals track...
Code.org
Event-Driven Programming and Debugging
Start programming in event-driven style. Scholars learn to place buttons on the user interface and use event handlers. They also learn to recognize errors in code and debug as necessary. This is the second lesson in the series of 21.
PBS
Hidden Messages in Spirituals
Slaves laboring in the cotton fields of the old South singing joyously may have convinced overseers that their workforce was happy and content, but in truth, these spirituals contained secret codes. After viewing a short video about...
NASA
Speaking in Phases
Hear from deep space. Pupils learn how satellites transfer information back to Earth. They learn about three different ways to modulate radio waves and how a satellite sends information with only 0s and 1s. Using sound, class members...
DocsTeach
Pearl Harbor Dispatch Analysis
Scholars play a historical version of the telephone game when they analyze the dispatch from the Pearl Harbor attack. The quick activity uses primary sources to help academics analyze an historical event. Young historians also complete a...
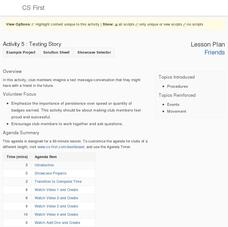
Google
Friends: Texting Story
Sometimes it's okay to text in school. Young computer scientists work in the Scratch program to write a text message conversation among friends. They use different sprites within the program to represent each side of the conversation to...
Discovery Education
Satellite Telemetry
Satellites require rockets to launch, but it doesn't take a rocket scientist to understand them. Future engineers learn about how satellites send data to Earth and how to interpret satellite images. They see how radio waves play a role...
TV411
Dependent and Independent Clauses Join Forces
Young grammarians are often confused by clauses, especially the difference between dependent and independent clauses. Clarify the confusion with a color-coded worksheet that clearly defines and illustrates the differences and then gives...
Code.org
Asymmetric Keys – Cups and Beans
Beans are for more than just counting! Introduce public key cryptography with cups and beans and ask scholars to use the beans to send secret numbers. Participants learn how this activity relates to public key cryptography and asymmetric...
American Institute of Physics
Optics and Anthony Johnson
Message sending has come a long way since the days of Morse code's dots and dashes. Young scientists study the research of optical physicist Anthony Johnson and his work in fiber optics, lasers, and the principle of total internal...
Code.org
Keys and Passwords
Scholars explore the relationship between cipher keys and passwords and as they learn more about the Vigenere cipher and continue to read from the book Blown to Bits in the seventh lesson of the series. They conduct an activity where...
Discover Da Vinci
Da Vinci: Machines Exhibition
Transportation devices, military devices, mechanical devices, entertainment devices. The inventions of Leonardo da Vinci are legendary. After viewing images of da Vinci's inventions, class members are encouraged to draft their own...
Code.org
HTTP and Abstraction on the Internet
Introduce your class to the layers of abstraction of the Internet with a activity on the HTTP protocol. Pupils review previous lessons on levels of the Internet, then investigate new high levels by examining the HTTP traffic on their own...
Northern Lights Special Education Cooperative
Lessons from The 7 Habits of Highly Effective Teens
As part of a study of Sean Covey, the author of The 7 Habits of Highly Effective Teens learners write autobiographical e-mails, hold discussions, create a collage, and compose a personal mission statement. Pupils then have a chance to...
Media Education Lab
The Ethics of Propaganda
What are the short and long-term consequences for consumers and producers of modern media propaganda? Class members ponder this essential question as their unit study of ethics of propaganda concludes. After examining two case studies,...
Mary Pope Osborne, Classroom Adventures Program
Civil War on Sunday
Reading Mary Pope Osborne's Civil War on Sunday? Here's a packet crammed with activities, exercises, reading guides, and project suggestions. A must-have for your curriculum library.